IT SERVICES

NETWORK CONSULTING
Our network consulting team has over 20 years of experience in network design and management. Our consultants evaluate the specific needs of the client, with the outlook that technology serves to support strategic objectives. The distinction of our service lies in our ability to recommend cutting edge technology that falls in step with business processes and overall corporate objectives. The solutions we recommend are there to optimize your business. Every solution caters to the needs of the client specifically – we do not believe in a one-solution-fits-all strategy nor do we believe in over-selling the customer on a “trendy” solution that has no direct benefit to the client.
OFF-SITE BACKUP
Our offsite back-up solution allows your business critical data to be continuously backed up and housed at a facility with bank-level security. All data is encrypted before it leaves your server and stored at our facility in encrypted form. The encrypted data is ready for download, provided the proper credentials are met, in the event of data loss. Offsite backup also provides the ability to restore files that have been deleted and our solution features a seven day rollback feature that allows a particular file to revert to a prior version.
Offsite backup should be a critical component of a company’s overall information technology strategy. Most companies rely on onsite tape backup, however this can be woefully inadequate as this type of backup is prone to many mechanical and human errors. Swapping tapes, faulty tapes, forgotten backups, compromised tapes are just a few of the problems. Also, many companies fail to take their tapes offsite leaving them vulnerable to theft and or damage in case of a disaster such as fire or flooding. Tapes transported offsite by someone are again subject to loss or damage – all too often briefcases get stolen. An automated offsite backup solution eliminates these risks while providing a complete, set-and-forget solution that ensures data is continuously backed up and available as needed.


NETWORK SECURITY
Security is at the forefront of the IT world. Creating and managing network infrastructure is critical to the operation of a business, but providing adequate/robust security protects and assures the integrity of business operations. A compromised network affects productivity.
We firmly believe that a network must be managed and defended at each gateway. Thus we offer comprehensive solutions in the following area:
- Firewall and Routers: Manage the flow of data traversing the network
- Antivirus, Anti-Spam and Anti-Phishing – Protect the end-user from Web Vulnerabilities
- Intrusion Detection/Intrusion Prevention Systems- Active and Proactively guard against attacks
- Security and Acceptable Use Policies- Help set guidelines and educate users on what they can and cannot do when using company IT resources (downloading and playing internet games is one of the leading causes of networks being compromised)
INFORMATION TECHNOLOGY AUDIT MANAGEMENT
A company’s IT department is usually responsible for configuring and maintaining the IT infrastructure while managing its key business processes such as a CRM or an ERP. A company with well-defined internal controls is able to identify and manage their IT related risks. Ability to manage and contain such risks is critical to ensuring compliance with regulations and mandates such as Sarbanes-Oxley Act (SOX) and Health Insurance Portability and Accountability Act (HIPAA).
Business Computing Solutions works with the IT as well as other departments to establish, test and maintain controls to assure compliance and security. These controls are typically derived from COBIT control processes and are designed to eliminate or mitigate IT related risks and form the basis for good IT governance.

OUR LATEST NEWS
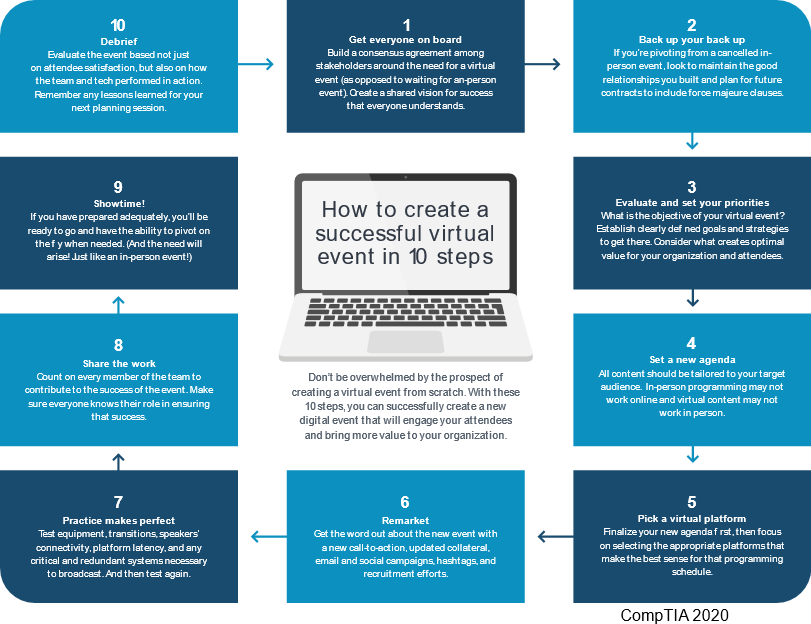
LEARN ABOUT OUR LATEST NEWS AND UPDATESSuccessful Virtual Event in 10 Steps
As the we continue in our remote world, we must come to terms with holding our events on an online platform. At first, it can seem daunting.
Read MoreCyber Insurance and Incident Response: What to Know
As cyberattacks rise, so does the call by business leaders and shareholders to be ready to respond to a cyber incident.
Read MoreFree Remote Emergency Kits
Free Emergency Remote Work Kits for Healthcare Providers, Educational Institutions, Municipalities & Non-Profit Organizations
Read More